Resetting admin login password for GMS Application Interface of SonicWall GMS Virtual Appliance on UMA
If you
have many SonicWall Firewall, it is not easy to manage without SonicWall GMS.
GMS have
two logins for System Interface and Application Interface.
System
Interface is to manage your GMS Hardware Appliance or Virtual Appliance.
Application
Interface is to manage your SonicWall devices in your network.
So, you
can contact to SonicWall Technical Support if you forgot the login password of
GMS System Interface. But to do so, you need valid support contract/license.
(So take note it and do not forget if you didn’t renew support contract/license.
:P)
For
application interface login password, you do not need Tech Support if you know
how.
As human
being, I am sure you will forget your password sometimes and here is how to
reset the GMS Application Interface Password.
First,
you will see like below if you forgot password.
You need MySQL Query Browser to access GMS Database in order to reset the password.
1.
Download
it from below link and run it on the machine which is located in same subnet of
GMS UMA or subnet which able to access of GMS UMA.
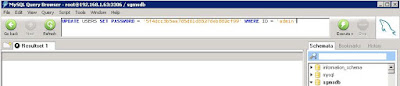
2. Open MySQL Query Browser:
3.
Log into the SGMSDB database using either the ‘root’ account or the
account you chose during Role Configuration:
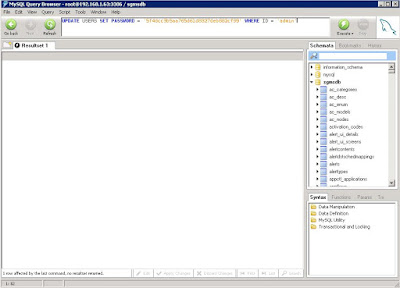
5. The Admin password has been
reset. You can now log in to the Application Interface using the
username ‘Admin’ with the password ‘password’:
(Be knowledgeable, pass it on then)




Comments
Post a Comment