It is not the end after only you can do installation , setup and configure the Fortigate unit as you wish.
Troubleshooting is also essential task you will need to perform one day.So, let's assume you was configured Fortigate unit as NAT/Route mode to operate for your network.
But the the Internet access was unable to connect from your network and need to find out what is it caused.
How to troubleshoot???
Use the following steps to find and fix the problem.1) Check the physical network connections between the PC and the FortiGate unit, as well as between the FortiGate unit and your ISP’s
equipment. The Unit Operation dashboard widget indicates the connection status of FortiGate network
interfaces (System > Dashboard > Status).
2) Check the ISP-supplied equipment such as Modem/Router to make sure it is operating correctly.
3) Verify that you can connect to the internal IP address of the FortiGate unit. (For exampe: ping test to Fortigate)
4) Check the configuration of the FortiGate interface connected to the Internal network.
5) Check the configuration of the FortiGate interface that connects to the Internet to make sure it includes the proper addressing mode such as Static IP Address mode or DHCP IP Address mode.
And also check each Address mode was configured proper IP address or netmask.
6) To verify that you can communicate from the FortiGate unit to the Internet, access the FortiGate CLI and use the execute ping command to ping an address or domain name
on the Internet. You can also use the execute traceroute command to troubleshoot connectivity to the Internet.
Connected
FW_TEST # execute ping google.com
PING google.com (173.194.38.160): 56 data bytes
64 bytes from 173.194.38.160: icmp_seq=0 ttl=54 time=2.8 ms
64 bytes from 173.194.38.160: icmp_seq=1 ttl=54 time=2.7 ms
64 bytes from 173.194.38.160: icmp_seq=2 ttl=54 time=2.7 ms
64 bytes from 173.194.38.160: icmp_seq=3 ttl=54 time=2.6 ms
64 bytes from 173.194.38.160: icmp_seq=4 ttl=54 time=2.6 ms
--- google.com ping statistics ---
5 packets transmitted, 5 packets received, 0% packet loss
round-trip min/avg/max = 2.6/2.6/2.8 ms
Connected
FW_TEST # execute traceroute google.com
traceroute to google.com (173.194.38.160), 32 hops max, 72 byte packets
1 58.185.137.217 0 ms 0 ms 0 ms
2 58.185.243.245 0 ms 0 ms 0 ms
3 165.21.255.37 1 ms 1 ms 1 ms
4 165.21.12.68 1 ms 1 ms 1 ms
5 203.208.192.105 1 ms 1 ms 1 ms
6 72.14.215.214 1 ms 5 ms 1 ms
7 66.249.95.122 2 ms 2 ms 2 ms
8 72.14.233.105 3 ms 2 ms 2 ms
9 173.194.38.1602 ms 2 ms 2 ms
7) Verify the DNS configurations of the FortiGate unit and the PCs on the internal network. You can check for DNS errors by pinging or using traceroute to connect to a domain name. If the
name cannot be resolved the FortiGate unit or PC cannot connect to a DNS server and you should confirm the DNS server IP addresses are present and correct. For example:
ping www.google.com
ping: cannot resolve www.google.com: Unknown host
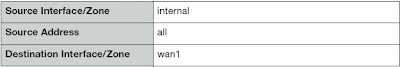
8) Verify the security policy configuration.
Go to Policy > Policy > Policy and verify that an internal -> wan1 security policy has been added. Check the Count column to see if the policy has been processing traffic.
Check the configuration of the policy to make sure it is similar to the following and that Enable NAT and Use Destination Interface Address is selected:
9) Verify the static routing configuration.
Go to Router > Static > Static Route and verify that the default route is correct. Go to Router > Monitor > Router Monitor and take a look at the routing monitor and verify that
the default route appears in the list as a static route. Along with the default route, you should see at least two connected routes, one for each connected FortiGate interface.
10) Disable web filtering.
If you have enabled web filtering in a security policy it may be blocking access to the web site that you are attempting to connect to. This can happen for a number of reasons.
A rating error could occur for a number of reasons, including not being able to access FortiGuard web filter ratings. To fix this problem, you can go to UTM Profiles > Web Filter > Profile, and in the default profile, select Advanced
Filter and enable the Allow Websites When a Rating Error Occurs option.
That's all. I hope you will be able to troubleshoot your Fortigate unit with above steps.
May you all happy.
(Be knowledgeable, pass it on then)
Comments
Post a Comment